Data Governance Roles & Responsibilities
Digital Transformation Steering Committee (DTSC)
A senior governance board responsible for providing strategic oversight and direction for the University’s digital transformation initiatives.
Responsibilities:
The responsibility of the DTSC is to approve the Data Governance Policy and related matters pertaining to policy development.
Data Governance and Data Strategy Workstream (DGDSW)
Operating under the DTSC, the working group within the DGDSW serves as an interdisciplinary team at the working level, responsible for overarching institutional data governance. Its membership, and operational details are defined in the DTSC Workstream4 DGDSW Terms of Reference.
Responsibilities:
- Develop and maintain an integrated institutional data platform aligned with the University’s Strategic Plan.
- Recommend data governance frameworks, policies, and lifecycle management standards for DTSC approval.
- Establish decision-making structures, approval workflows, and communication plans for governance initiatives.
- Foster secure data collaboration with external partners and internal stakeholders to eliminate duplication and maximise resource efficiency.
- Advise the DTSC on risks related to data systems, analytics practices, and compliance gaps.
Data Trustee
Data Trustees are typically executive roles, such as unit Heads and Directors who hold ex-officio responsibility for planning and decision-making related to institutional data. Data Trustees for Restricted data should hold a Vice President level position, while the approval authority related to Restricted data should rest with the President. The President shall appoint individuals when there is any ambiguity regarding the role of Data Trustees.
Responsibilities:
- Ensure alignment of the data strategy with other University information management initiatives and strategies.
- Ensure that data assets are coordinated across the University at the highest level to ensure maximum benefits to the University’s missions and vision.
- Oversee implementation and compliance with this Policy.
- Define access control based on user roles, departments, or projects in respective domain.
- Review and provide advice on escalated cases from Data Stewards.
Data Steward
Data Stewards are leadership roles such as managers and assistant/associate directors who have direct operational level responsibility for the management of one or more types of institutional data.
Responsibilities:
- Ensure that data in their respective domain is accurate, up-to-date, and protected from loss and unauthorised access.
- Ensure that data are appropriately classified and reclassify them if necessary.
- Ensure that staff within their organisational unit have the appropriate level of access to data according to their assigned duties, roles and responsibilities.
- Ensure that an up-to-date Data Inventory is maintained in their respective domain.
- Define and monitor the data retention period, and develop processes to securely delete or archive data at the end of the retention period for approval by the DTSC.
- Assess and process data requests.
- Escalate data request cases to Data Trustees for advice if needed.
- Ensure that the requirements of this Data Governance Policy and related procedures are adhered to within their organisational unit.
- Ensure regular updates of the supplementary documentation – Data Governance Role Directory.
Data Custodian
Data Custodians are staff of Data Stewards and have operational responsibility for the capture, maintenance, dissemination, and storage of institutional data in their respective data domains.
Responsibilities:
- Coordinate both within and outside their data domain to ensure data is transmitted efficiently and securely between business areas.
- Ensure that data is collected in a timely, complete, and appropriate manner.
- Collaborate with Data Guardians to ensure that data access is monitored, and breaches are reported in a timely manner.
- Maintain and regularly update the Data Inventory for each data domain under their responsibility, including data source, data definition, and uses of the data.
- Alert Data Stewards of any need for data reclassification.
- Securely delete or archive data at the end of the retention period under the process developed by Data Stewards.
Data Guardian
Data Guardians provide support to all data governance roles. They are typically specialised personnel from the Office of Information Technology, Estates Office, and the Office of Institutional Research and Planning, responsible for monitoring and protecting data across the University.
Responsibilities:
Estates Office
- Implement and ensure security to protect data centers and office spaces from unauthorised access, particularly where sensitive data is stored.
- Ensure that data storage areas are equipped with appropriate environmental controls, such as temperature and humidity regulation, to protect hardware from damage.
- Regularly inspect and maintain the physical infrastructure to prevent vulnerabilities that could compromise data security, such as faulty locks or broken windows.
- Ensure the response plans for incidents such as fires, floods, or other disasters that could affect data security is updated and drilled regularly.
Office of Information Technology
- Manage authorised data access and oversee the secure transmission, data security and storage of data.
- Deploy and enforce access control lists and user permissions for Restricted, Confidential, and Internal institutional data.
- Maintain activity logs to document access events for security assessments and investigations for all Restricted and Confidential institutional data.
- Ensure a disaster recovery plan is updated and drilled regularly.
Office of Institutional Research and Planning
- Monitor data quality and alert respective Data Stewards of data quality issues.
- Regularly review roles and access rights to ensure alignment with organisational changes, the evolution of roles, and regulatory updates.
- Report on updates and implementation status of this Policy for all data assets across the University to the DTSC every six months.
- Conduct training sessions for staff in all data governance roles to raise awareness of the data governance policy, ensure understanding of individual roles and responsibilities, and provide relevant knowledge of data governance tools.
Important Notice
All data governance roles must ensure compliance with relevant laws and regulations within their scope of responsibilities, including but not limited to the Personal Data (Privacy) Ordinance.
Data Classification
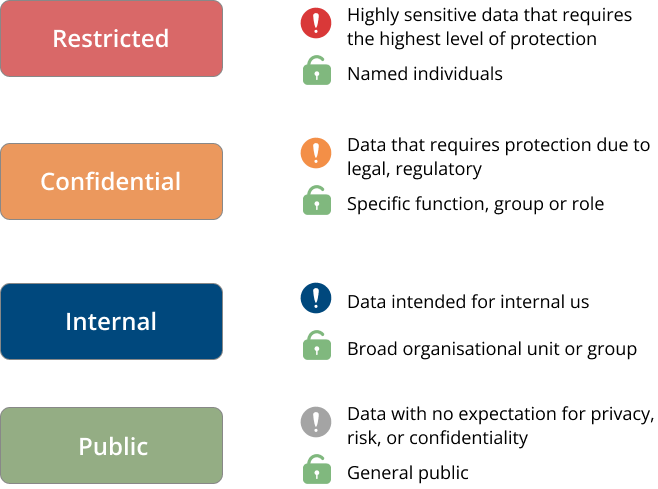
1. Data classification in this framework refers to the categorisation of data based on its level of sensitivity and criticality.
2. All institutional data within the University shall be categorised into distinct access tiers, each shall be defined according to the sensitivity, confidentiality, integrity, availability, and the required protection measures. These access tiers will determine the authorisation required to access specific data sets.

Sensitivity Level
Criticality Level - Critical Data Element (CDE)
All institutional data shall be designated as either a Critical Data Element (CDE) or not, based on an assessment of the strategic value, operational importance, and compliance requirements:
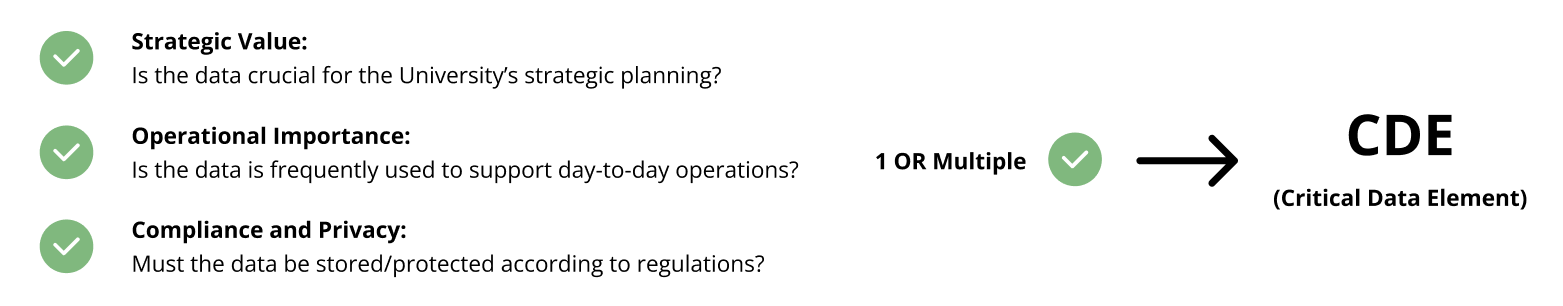
a. Strategic Value: Data that is crucial for the University’s strategic planning and decision-making processes.
b. Operational Importance: Data that is regularly used to support the University’s day-to-day operations and service delivery.
c. Compliance and Privacy: Data that must be stored and protected in accordance with legal or regulatory requirements, including data containing personally identifiable information.
Metadata Management
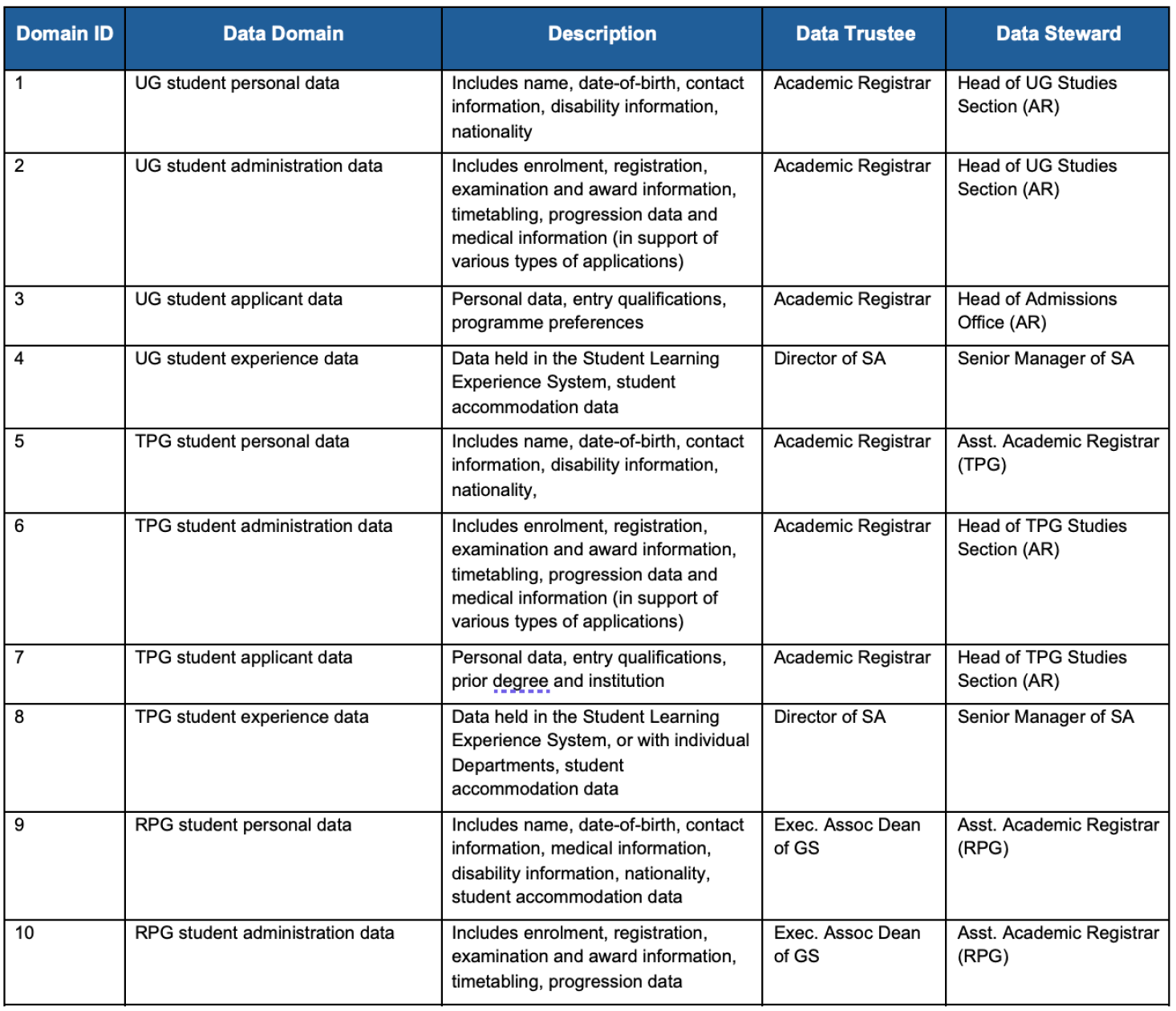
Data Domain Directory
What data domains does the University encompass?
Data domain are the high level categories of institutional data to assign accountability and responsibilities effectively.
Data Governance Role Directory
ConfidentialThe updated role directory contains individual contact information.
Data Inventory and Asset Management
InternalThe templates and instructions for preparing the data inventory.
Data Request Procedure
Data Request Purpose
- Student data and learning data management
- Research data management
- Collaboration with, or service provision by external Data Users
- Compliance
- Investigation
- Statistical purposes and institutional analytics
- Internal operations
Data Request Approval Principles
- Data requested must be relevant to the purposes of use
- Restricted, Confidential and Internal institutional data shall not be used for teaching and learning, research purposes or Collaboration with, or service provision by external data users as outlined in the Approval Authority and Data Classification Tier table
- The data being requested or derived outputs shall not lead to unnecessary identification of an individual
- The data requested or derived outputs shall not cause possible prejudice or bias against a certain group of individuals or lead to an adverse impact on the reputation of the University or any other individuals
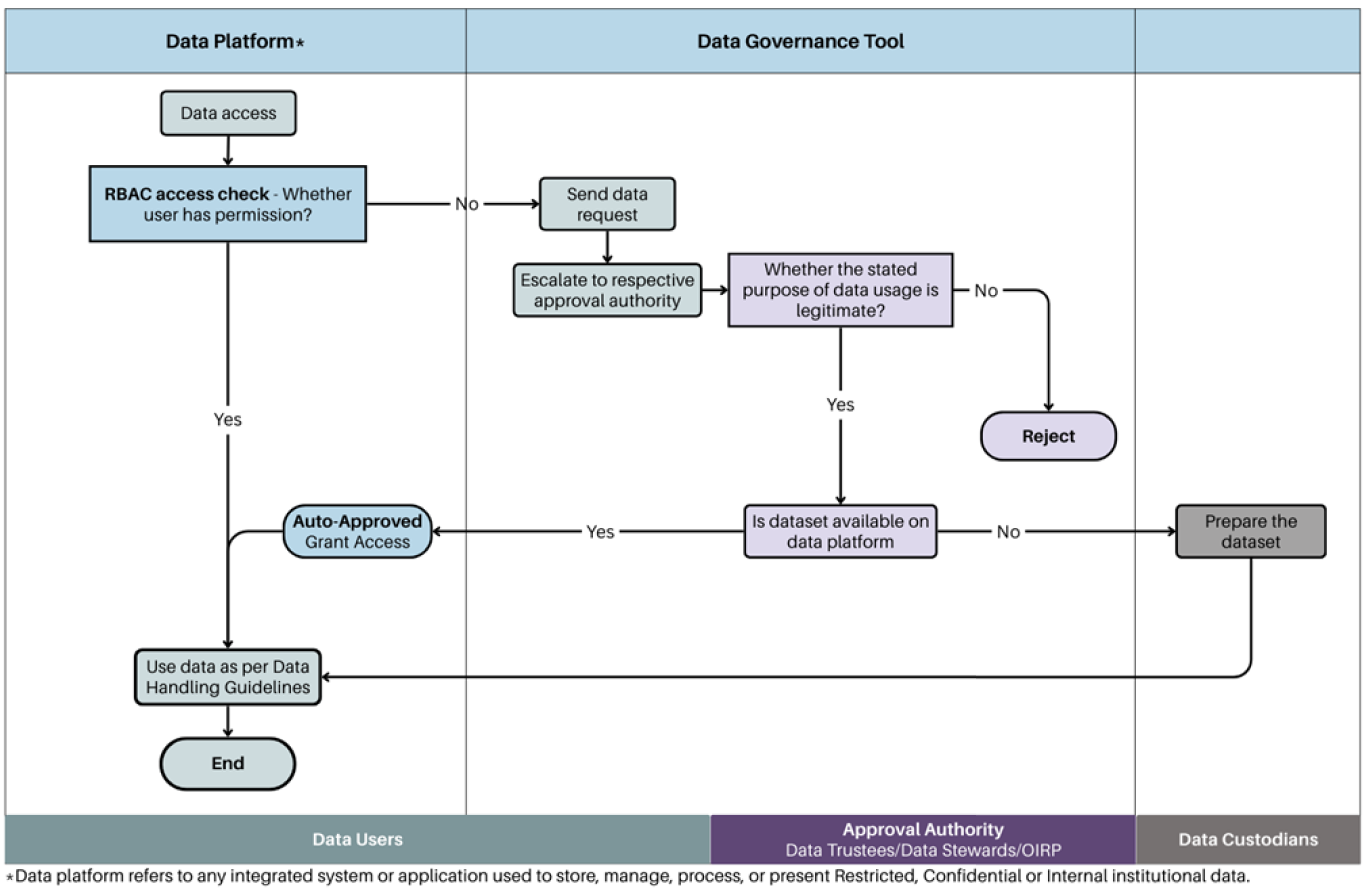
Data Request Approval Authority

Data Request Approval Workflow
Data Quality Management
- Detailed data quality guidelines, principles, and roles and responsibilities can be referenced in the Supplementary Documentation – Data Quality Policy.
- The data quality of all Critical Data Elements must be regularly assessed and monitored.
- A data asset is deemed valid only if it complies with the data quality requirements established within this framework.
Dimensions of Data Quality
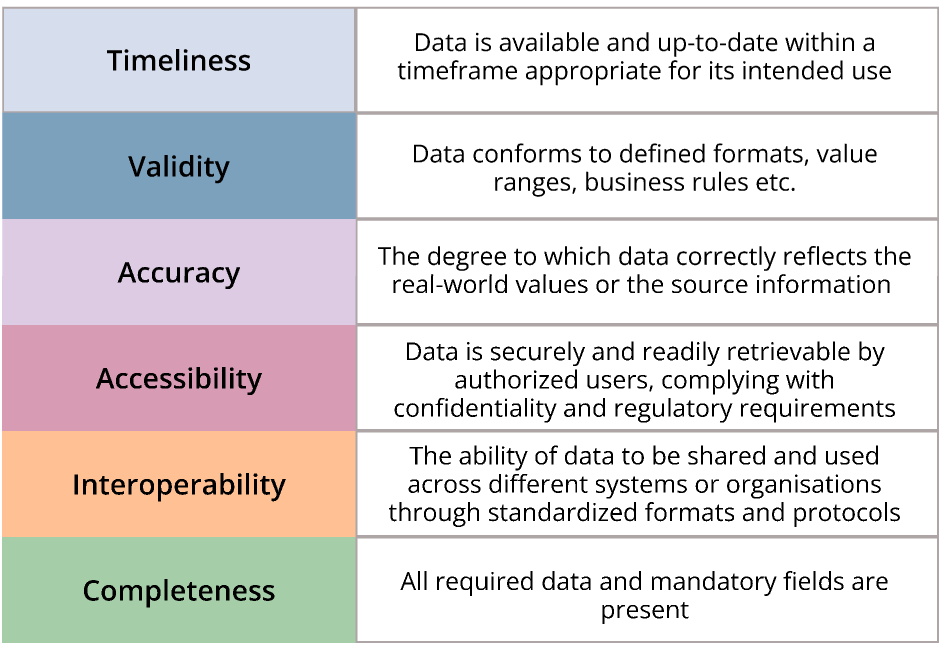
Define Business Rules and Data Quality Rules
- Business rules are statements that describe or imply expectations about the quality characteristics of data.
- Data quality measurements that describe whether data is fit for use should be developed in relation to known uses and measurable rules based on six dimensions of data quality defined in this framework.
- The known usage of data, including input and output requirements of a business process should be documented at the data collection stage.
- Data quality rules should be documented in a consistent format as shown in the Appendix and managed as metadata.
- Data quality rules need to be accessible to all authorised data users.
Access and Measure Data Quality
- Data quality rules should be implemented into systems and specified tools to ensure continuous monitoring of data quality.
- Knowledge of known data quality issues should be applied to manage risk. Measurements should be put in place to monitor functions similar to those that have had data quality issues.
- The results of assessments should be communicated to data stewards, data custodians and authorised data users.
Data Quality Issue Remediation and Data Quality Improvement
- Identified data quality issue must be tracked and assigned to a designated individual, who will be accountable for remediating the issue at its source system.
- Data quality issues should be remediated in a sequence that prioritises the criticality of the data.
- Discovery and refinement of rules is an ongoing process.
Roles and Responsibilities
- Approving and publishing the data quality policy
- Reviewing and approving the list of data criticality
- Reviewing criticality levels to data domains in accordance with the guidelines and submitting them to the DTSC for approval
- Developing and overseeing compliance with the data quality policy
- Monitoring data quality, performing data profiling and ensuring that reports on data quality status are communicated to the respective Data Stewards
- Establishing data quality authentication standards
- Identifying and recommending technology solutions to support the data quality process
- Ensuring that previously agreed-upon improvement actions are implemented and monitored on a regular basis
- Defining business rules and establishing a data quality baseline for status indicators
- Overseeing the process of data quality issue remediation and ensuring that data quality issues are remediated at the root cause within the specified timeframe
- Developing data quality metrics with the approval of Data Stewards
- Identifying data quality issues and ensuring they are properly documented
- Conducting root cause analysis on identified data quality issues and proposing remediation plans subject to the approval of Data Stewards
- Implementing the necessary actions to remediate data quality issues, with the approval of Data Stewards and testing the fixes to ensure the issues are resolved
- Ensuring that the data they create, manage and use is of high quality, in accordance with the Data Quality Standards
- Taking action to resolve or request the resolution of data quality issues, ensuring that these issues are submitted to the respective Data Stewards
Data Lifecycle Management
The process of managing data from its creation to its deletion. It involves collecting, storing, accessing, using, and eventually disposing of data in a way that keeps it organized, secure, and compliant with regulations.
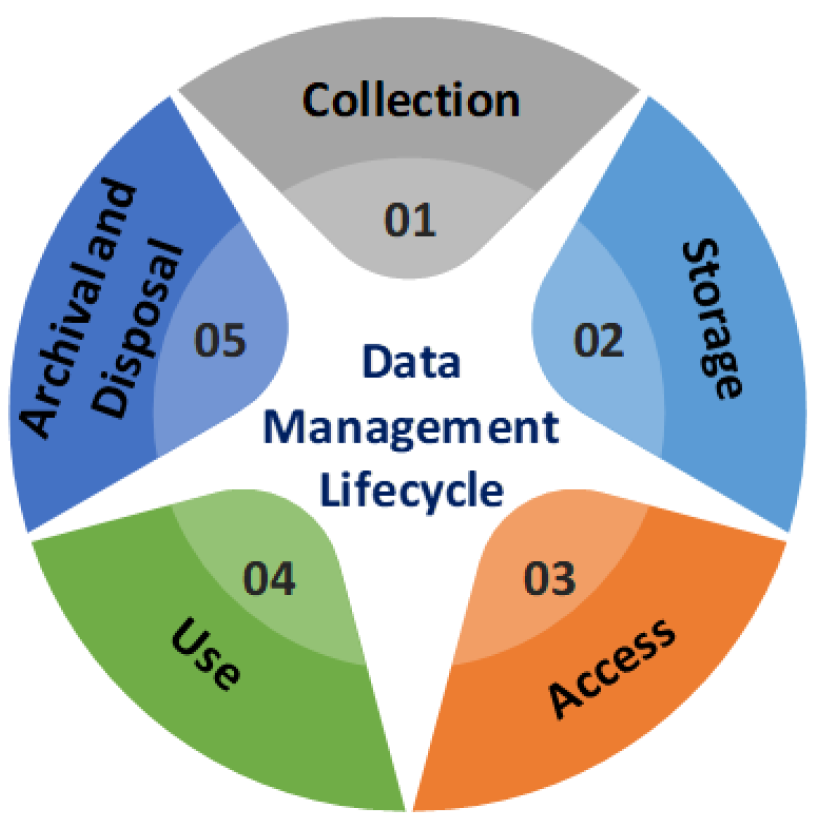
01 Collection
- Data Guardians are tasked with sharing the data definitions with authorised users via specified data governance tools or platforms to ensure interoperability.
- Data Stewards are responsible for defining data definitions and developing procedures to guarantee that the data collected within their domain conforms to the data quality framework established in this Policy. Data Stewards shall ensure that data collected are classified according to the four tiers stipulated in this framework.
- Data Custodians, with the approval of Data Stewards and respective Guardians, must ensure that information technology systems used to capture and update institutional data incorporate appropriate validation checks. These checks maintain data quality and prevent unauthorised creation, alteration, or deletion of data.
- For Confidential, or Internal institutional data, the data definition, data retention period, as well as procedures and methods for collection shall be approved by the Data Trustees to ensure consistency. For Restricted institutional data, the approval authority shall rest with the President. All data definitions shall be developed by Data Stewards and Data Custodians, and stored in a designated data governance tool managed by OIRP.
02 Storage
- Data Stewards, with support from Data Custodians and Data Guardians, shall identify the official data storage location for each type of institutional data under their respective data domain. Working with Data Custodians, Data Stewards should ensure that data classified as Restricted, Confidential, or Internal are kept secure, using, where applicable, dedicated and reliable storage together with an appropriate level of physical and/or digital security. Regular review and reclassification of data shall be conducted as needed.
- In situations where Restricted, Confidential institutional data requires transmission and storage, Data Custodians, with support from Data Guardians, should ensure that an appropriate level of encryption is adopted to ensure the confidentiality of the data. Should the storage of Restricted or Confidential institutional data involve physical documents, Data Custodians should ensure the documents are marked with appropriate designation.
03 Access
- Data Stewards must ensure that proper access rights to institutional data are assigned to designated Data Custodians and Data Users based on the appropriateness of the latter’s role and the intended use/function, and that such authorisation is reviewed on a periodic basis.
- Data Guardians must document all approved access to Restricted, Confidential institutional data. This access documentation should be retained for at least one year or longer if required.
04 Use
- Institutional data is available to Data Users carrying out their University responsibilities on a need basis. An individual interested in utilising institutional data for any other purpose must make a formal data request following the procedure outlined in the supplementary documentation - Data Request Procedure.
- All staff of the University must comply with all requirements for handling institutional data or information during their employment.
- Data Stewards are required to develop a Non-Disclosure Agreement established by the General Administration Office (GAO) with external Data Users regarding the proper use and protection of Restricted, Confidential, or Internal institutional data. Please refer to the Policy and Procedures on Commitment Approval and Contract Execution for guidance on the procedure.
05 Archival and Disposal
- Data Stewards shall determine the archiving, depersonalising, and strategy for preserving historical data for each type of institutional data in their respective domain.
- Data Stewards shall ensure that proper policies and procedures are in place for the secure disposal of all institutional data whether in physical or digital form.
- Upon the expiry of data retention periods, and with approval from DTSC (or the President, in the case of Restricted data), data shall be securely deleted or archived as needed by Data Custodians. Data Custodians shall document and report the completed deletion to the Data Stewards for verification and record-keeping. Data Users who have been granted access to the data must securely delete any copies or extracts of the data after they have completed the purpose for which access was granted.
